In This Article
 TrueCrypt is free software for on-the-fly-encryption (also known as real-time encryption). “On-the-fly” refers to the fact that the files are accessible immediately after the key is provided, and the entire volume is typically mounted as if it were a physical drive, making the files just as accessible as any unencrypted ones. On-the-fly encryption also means that files are encrypted or decrypted right before they are loaded or saved, without any user intervention. No data stored on an encrypted volume can be read (decrypted) without using the correct password or correct encryption key. Until decrypted, a TrueCrypt volume appears to be nothing more than a series of random numbers. The entire file system is encrypted (i.e., file names, folder names, contents of every file, and free space).
TrueCrypt is free software for on-the-fly-encryption (also known as real-time encryption). “On-the-fly” refers to the fact that the files are accessible immediately after the key is provided, and the entire volume is typically mounted as if it were a physical drive, making the files just as accessible as any unencrypted ones. On-the-fly encryption also means that files are encrypted or decrypted right before they are loaded or saved, without any user intervention. No data stored on an encrypted volume can be read (decrypted) without using the correct password or correct encryption key. Until decrypted, a TrueCrypt volume appears to be nothing more than a series of random numbers. The entire file system is encrypted (i.e., file names, folder names, contents of every file, and free space).
The above description may not seem exactly clear to you. It didn’t to me, either. All I can say is I love this software but had to figure it out by giving it a try. Now that I understand how it works, I find it very useful. For a video explaining the ins and outs of TrueCrypt, check out TechRepublic’s File encryption made simple with TrueCrypt.
Since USB flash drives are easily lost, left or stolen, they are great candidates for using TrueCrypt. Here are the steps:
Step 1: Download and Install TrueCrypt
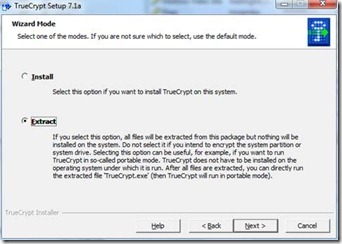
Download TrueCrypt directly to your USB drive. When you click to install you will see this screen:
Choose the second option. This will create a TrueCrypt folder on your USB drive but will not install anything. Next, choose the location to extract the files.
Note that by default the program will try to install the files in a folder called TrueCrypt (see above). Either change that to the default directory (in this case E:\) or after the install just move the created files (or at a minimum the .exe and .sys files) to the root directory. If you don’t do this you may get a “The process cannot access the file because it being used by another process” error in the next step.
Step 2: Create a TrueCrypt encrypted container on your USB drive
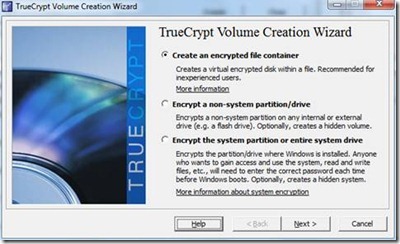
Create a TrueCrypt encrypted container on your USB drive by running the TrueCrypt Format.exe file. You’ll see the following screen:
Choose “Create an encrypted file container” and click Next. You’ll see:
Choose “Standard TrueCrypt volume” and click Next. You’ll see:
Click “Select File…” and browse to the root of the USB stick. Type in whatever filename you wish to create (e.g., JMB above) and click Save, then click Next. You’ll now see:
Leave the default “Encryption Algorithm” as AES and likewise leave the default “Hash Algorithm.” Click Next which will bring you to the following screen:
Enter a “Volume Size”. Notice you can’t use decimal points so it is easier to specify gigabytes in megabytes instead (e.g., 3000MB = 3GB). One recommendation here is to NOT fill up the whole USB stick. I would only make a container that fills about 75-90% of your USB drive since it’s usually good to have some free space that you can use for files you don’t need encrypted or for working with systems that can’t run TrueCrypt. Click Next to get to this screen:
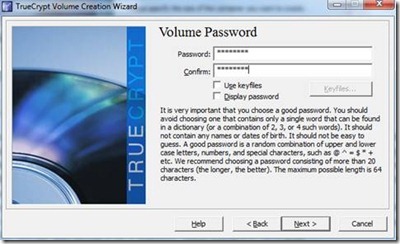
Enter a password for the encrypted container and click Next which brings up the following.
On this screen you will need to move your mouse around the TrueCrypt window for a while to help randomize the creation of the encryption key and then click Format. It will take a bit of time to format your drive but when it finishes just click Exit and you are finished with the setup.
Step 3: Setup a TrueCrypt Traveler Disk
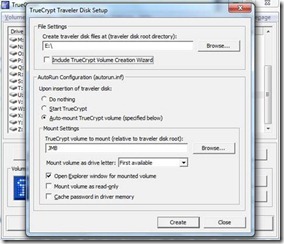
Run the TrueCrypt executable file created in the first step. This will open the main screen. Go to “Tools” then “Traveler Disk Setup.” You will see this screen:
Change “Create traveler disk files at” to your current USB drive letter. There is no need to check the “Include TrueCrypt Volume Creation Wizard” box since we just went through that process. You can choose whichever “Autorun Configuration” option you prefer but choosing the Auto-mount option will allow you to be automatically prompted to mount the encrypted “container” when you insert your removable drive into a computer that supports this feature (some computers have this disabled). Next, specify the name of the encrypted “volume” that we created above, in this case JMB. Finally, just press the Create button and the OK button once finished.
Step 4: Use your USB drive
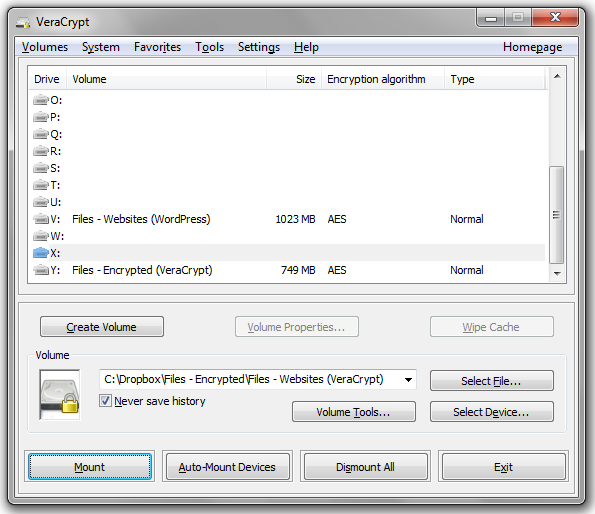
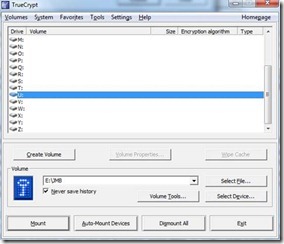
To start moving files onto the new container (“volume”) you created above on your USB drive, simply run the Truecrypt.exe file.
Now select any open drive letter you feel like using and use the “Select File…” button to select the volume created in the steps above (e.g., JMB). Then click Mount.
This opens and decrypts your volume file. You will now be able to see it in your Windows Explorer.
Now simply drag any files to the new drive with your mouse. When you’re done, just dismount the container which closes and encrypts it again.
Some final notes:
1. You need to have administrator rights to use TrueCrypt. On your own computer this will most likely not be a problem but if you try to use a computer at work or in a cyber café it might be a different story. There is no workaround for this.
2. On all my USB drives I like to include (unencrypted) a basic text file named IF FOUND - CONTACT. In it I ask anyone who finds the USB drive to please contact me and then I list my name, email address and phone number. Since you are probably more likely to forget your USB drive then to have it stolen, this will allow any nice person who happens to find it to contact you to return your drive.
3.  When you exit from TrueCrypt it doesn’t always fully close the program. In other words, it stays in memory and you can see it in the system tray. You will need to fully close it (from the system tray) to successfully eject your USB drive.
When you exit from TrueCrypt it doesn’t always fully close the program. In other words, it stays in memory and you can see it in the system tray. You will need to fully close it (from the system tray) to successfully eject your USB drive.
4. You may have noticed in the beginning of the second step the option to encrypt an entire system drive. As I mentioned already, it is usually a good idea to leave some unencrypted space on your drive. The other benefit is that if you ever decide to stop using TrueCrypt on the drive you can just delete all the files and you’ll be ready to go. This won’t be true if you choose to encrypt the entire drive.
Click to See or Add Your Own »









TrueCrypt!!!?? I need this.