In This Article
| Last Updated: October 13, 2023 (originally published December 6, 2019) |
A password is often the foundation which supports your digital privacy efforts. The way you approach passwords, as with everything privacy related, is a tradeoff of convenience and security.
The key things to understand about passwords are their strengths and weaknesses, how to store and use them, and how to create good ones. It’s also good to consider related strategies like multi-factor authentication, usernames, security questions, social login, and passkeys.
Of course, not all passwords are equally important. The ones you use for your electronic devices, email and financial accounts, and other accounts that store sensitive information are most critical. Other accounts which require a password but don’t store much personal information are less critical. You may choose to employ different strategies depending on the type of the account being protected or you may treat all accounts as sensitive and use the same strategy for creating, storing and accessing all your passwords.
Let’s get started with a detailed look at everything you need to know to make the right password choices.
How Do Our Password Protections Fail?

Passwords are a security measure, not a guarantee. Below I will go into detail about how bad actors defeat your passwords. I think it’s interesting and also helps illustrate how important this security measure can be in protecting your private information and data.
Hackers and other bad actors typically gain access to your passwords—and thus your accounts—by the following methods:
- Guessing the password because it is simple (e.g., “password,” “12345,” your son’s birthday)
- Guessing the password by reuse (you reused credentials from a compromised account with other accounts)
- Getting your password from a third party (usually by hacking a company or website or buying passwords from someone that did)
- Stealing your password with a keylogger or other form of malware
- Getting your password via social-engineering techniques (the art of manipulating people into divulging confidential information; phishing is a common form of social engineering)
- Stealing your password physically (if you wrote it down, either on paper or in an unprotected file that a thief can access)
- Cracking your password using a variety of methods
- Getting your password via a linked account; for example, someone gets access to your email account or mobile phone, which is then used to reset your account passwords
- Resetting your password using social engineering
Some of these methods are a bit beyond your control (or, at least, are difficult to control) but most are things you can take active steps to avoid. Since the focus of this article is password security, let’s take a bit of a deep dive into how hackers crack passwords.
Targeted Attack vs. Large-Scale Attacks
If you aren’t tech savvy or if you have watched too many Hollywood movies, you may think your biggest worry is that someone will target you personally. You may also reason that you aren’t really important or interesting enough to make a worthwhile target. But that’s simply not how you are most likely to have your accounts compromised. In fact, hackers get access to most accounts via large-scale server breaches which expose thousands or even millions of account details. Hackers then attack those compromised accounts with no specific malice toward any single person.
Of course, sometimes a hacker targets an individual. If so, the attacker usually uses one or more of the methods I already listed, like phishing or physical access to an account list or electronic device. If a hacker doesn’t have knowledge of your account passwords but has access to your personal information, he or she might use that information to make educated password guesses. For example, a smart hacker will test details from your address book, meaningful dates, and any other personal information available. Postal codes and birthdays are common password endings. If a hacker has access to your device, he or she will index it and create a list that includes every printable string, including deleted files. If you ever saved an e-mail or file with a password, this process will grab it. And it will speed the process of guessing your password.
But this is not the way most accounts are hacked. That’s because even in the best of circumstances, without knowing the actual username and password, hacking one person’s account is a high-risk, low-reward activity. This makes sense when you consider that trying to guess a password on a login page is a slow process. In addition, these days, most accounts limit the number of login attempts allowed. That most passwords are obtained from large-scale server breaches means that hackers may get your account details through no fault of your own. But that doesn’t mean you are defenseless. To understand how you can protect yourself, it’s helpful to first understand the mechanics of password cracking.
Password Cracking
You may wonder why we say that passwords are “cracked” rather than hacked. We do so because passwords are almost never stored in plain text (which would be an inexcusable lack of security). Instead, they are stored using one-way cryptographic hash functions, which obfuscate the original password by generating a unique string of characters for each unique string of plaintext. For example, 5f4dcc3b5aa765d61d8327deb882cf99 is the resulting text after applying the widely used MD5 hash function to the word “password.”
| Delve Deeper: For more insight into how hackers crack passwords, check out an excellent collection of articles by Ars Technical. Nate Anderson’s article, “How I became a password cracker,” discusses how he learned how to crack passwords and offers a step-by-step illustration of the process. Dan Goodin has a series of articles that helps explain how easy it has become to crack passwords, including “25-GPU cluster cracks every standard Windows password in <6 hours,” “Why passwords have never been weaker—and crackers have never been stronger,” and “Anatomy of a hack: How crackers ransack passwords like ‘qeadzcwrsfxv1331’.” They are quite old now, but still very informative. |
Hash functions are interesting in that they only work in one direction. You can’t mathematically reverse a hashed string of text. The only way to discover the original text is to “crack” the hashed text by generating guesses and hashing those through the same cryptographic function. When the output of a particular guess matches hashed text from a compromised database, the corresponding password has been cracked.
There are different hash functions. Some are “fast” (e.g., MD5, SHA1, SHA2, SHA3) and some are “slow” (e.g., Bcrypt, PBKDF2, SHA512crypt). Those designations refer to how much computing effort and time is required to apply the hash function. The process for cracking a password table is the same regardless of the hash function used, but faster hashes require fewer computing resources (and, thus, time) compared to slower ones.
For example, a hacker with an inexpensive computer can cycle through billions of guesses each second when trying to crack tables created with fast hashes. He or she might only cycle through millions or maybe even only thousands of guesses when trying to crack tables created with slow hashes.
| Salt? To further secure passwords, companies often “salt” their hashes — that is, they add a bit of random data to the text before applying the hash. This way, the hash won’t match the actual password, unless the salt is removed first. Without a salt, identical passwords will map to identical hash values, which could make it easier for a hacker to guess the passwords from their hash value. Salting also makes it difficult for a hacker to use rainbow tables or to determine if a person has used the same password for multiple systems. For these reasons, salting is good but it does not actually slow down the cracking of a single hash and does little to slow down attacks on small numbers of hashes. |
Ideally, everyone would use slow hash functions, but many companies still use the faster ones and there is usually no way to know which one a site uses when you create a password. Even though you can’t control which hash a site uses, it’s useful to understand this bit of technical trivia because any time you see a tool that tells you how strong your password is, it is making assumptions about the type of hash being used. A strong password for an account created with a slow hash might be a relatively weak password for an account created with a fast hash.
With that background, let’s consider the various methods hackers can use to crack a password. What seems most logical to a layperson is a brute force attack, whereby a hacker tries every combination of characters, numbers, and symbols of various lengths. This is often what articles that discuss passwords consider when explaining how a password becomes exponentially more difficult to crack when you make it stronger.
But here’s the thing. Most cracking attempts don’t use brute force attacks, except to crack relatively short passwords. That’s because it takes too much time. Rather, for longer, more complicated passwords, hackers take advantage of human behavior and what they learn from previous security breaches. In fact, the collective body of passwords from previous hacks has led to an enormous collection—at least hundreds of millions—of known passwords. Since many people reuse passwords and since many people choose the same—usually weak—passwords more often than you would think, hackers use these as first guesses. They have also used this collection of known passwords to gain insights about how humans choose passwords, which doesn’t vary much across languages or cultures. These insights have let hackers vastly improve their cracking tools.
| A Little Password Cracking History Prior to 2009, password cracking didn’t have many advanced techniques. In that year, a hacker breached the server for the popular service RockYou, leaking account details—in plain text—for over 32 million users. That gave hackers the first big insight into how people create passwords and it led to the rapid development of the password-cracking world. Suddenly, hackers had incredible input values and insights for cracking password databases. Every password leak since then has increased the collection of known passwords and the understanding of how people create passwords. |
For example, many people take a similar approach when trying to create strong yet simple passwords. They start with a name, place, or common word as the base (women often use personal names and men often use hobbies, interests, and sports teams). They then try to strengthen this base word with various obfuscation techniques. One of the most common of these is to capitalize the first letter of their base word. Another common technique is to add numbers (e.g., a birthday) or non-alphanumeric characters (e.g., “###”) to the base word, usually at the end, the beginning, or both, but rarely in the middle. Another technique is to transform the base word using special characters. For example, “superior” or “priceless” becomes “sup3r1or” and “pric3l3$$.” Yet another common technique is to append a mirror image of the chosen word, so “battery” becomes “batteryyrettab” and “password” becomes “passworddrowssap.”
Techniques like these may give the appearance of strong security, especially when they result in long passwords, but that’s an illusion because hackers use them to make better password guesses.
Putting everything together, let’s consider the basic process of password cracking. Once a hacker has a compromised list of passwords they can work on offline, he or she takes a logically structured approach to guessing passwords. Each guess is hashed with the hash function used by the site that was compromised, a salt is applied if necessary, and the resulting hash is compared to all the hashes in the database. If a match is found, that entry is removed to reduce further efforts and added to the known list.
The first set of guesses uses a huge list of words—including dictionary entries, foreign words, names, profanities, acronyms, and more. The hacker next tries different versions of these words using combinations of upper- and lower-case letters. He or she then tries a huge list of passwords discovered over the years in previous breaches.
This might seem like a lot of effort, but since even modest computers might test billions of guesses per second, time isn’t a big concern for this type of dictionary attack.
After this first set of guesses, the hacker makes new attempts by running each word through permutation filters and rules engines to mimic the techniques mentioned above that hackers know people use to generate passwords. Given today’s incredible computing power, it’s easy for skilled hackers to make an amazing number of guesses in a short amount of time. But software that applies common cracking datasets and techniques makes for a cut-and-paste exercise that even script kiddies can perform with ease.
Strong Passwords
So, what is the key takeaway from the discussion of password cracking? First, passwords become relatively easier to crack as computing power and accumulated cracking knowledge increase. Second, because brute force attacks require a lot of time and computing resources, most hackers don’t use them for strong passwords. Taken together, those two things mean that the best way to ensure your password is secure is to make it strong, measured by both current and future standards. Practically speaking, that means three things: it needs to be long (12 or more characters, but more will ensure it is strong further into the future), it needs to use a large character set (letters, numbers, and special keyboard characters), and it needs to be truly random.
| Strong Passwords Aren’t Enough. Password strength is important, but it won’t help much if your password is compromised through social-engineering techniques (e.g., phishing), is reused from another account that was successfully compromised, is reset by hackers who gain access to your email or phone, or is stolen because you store it an insecure way. |
Assuming you choose long, random text for your password, you might like to know how strong it is. Many websites offer password strength meters on the registration page. These are useful, but they usually assume your password is random. If it is not or you are using one of the well-known obfuscation techniques, the strength reported will be unreliable. You can find a better option at OnlineDomainTools. It has specific fields to show your password’s variation in characters, its appearance in dictionaries, and the time it would take for a brute force attack to crack it. Alternatively, a simpler option is the How Secure Is My Password tool.
If you use a password manager, which I highly recommend and will discuss later, most can create strong passwords and show you how strong your existing passwords are.
| Entropy. Password strength is often specified in terms of information entropy, which is measured in shannon (Sh). You can think of it as the minimum number of bits necessary to hold the information in a password. Instead of the number of guesses needed to find the password with certainty, the base-2 logarithm of that number is given, which is commonly referred to as the number of “entropy bits” in a password, though this is not the same quantity as information entropy. A password with an entropy of 42 bits calculated in this way would be as strong as a string of 42 bits chosen randomly, for example, by a fair coin toss. Put another way, a password with an entropy of 42 bits would require 242 (4,398,046,511,104) attempts to exhaust all possibilities during a brute force search. Thus, increasing the entropy of the password by one bit doubles the number of guesses required, making an attacker’s task twice as difficult. On average, an attacker will have to try half the possible number of passwords before finding the correct one. |
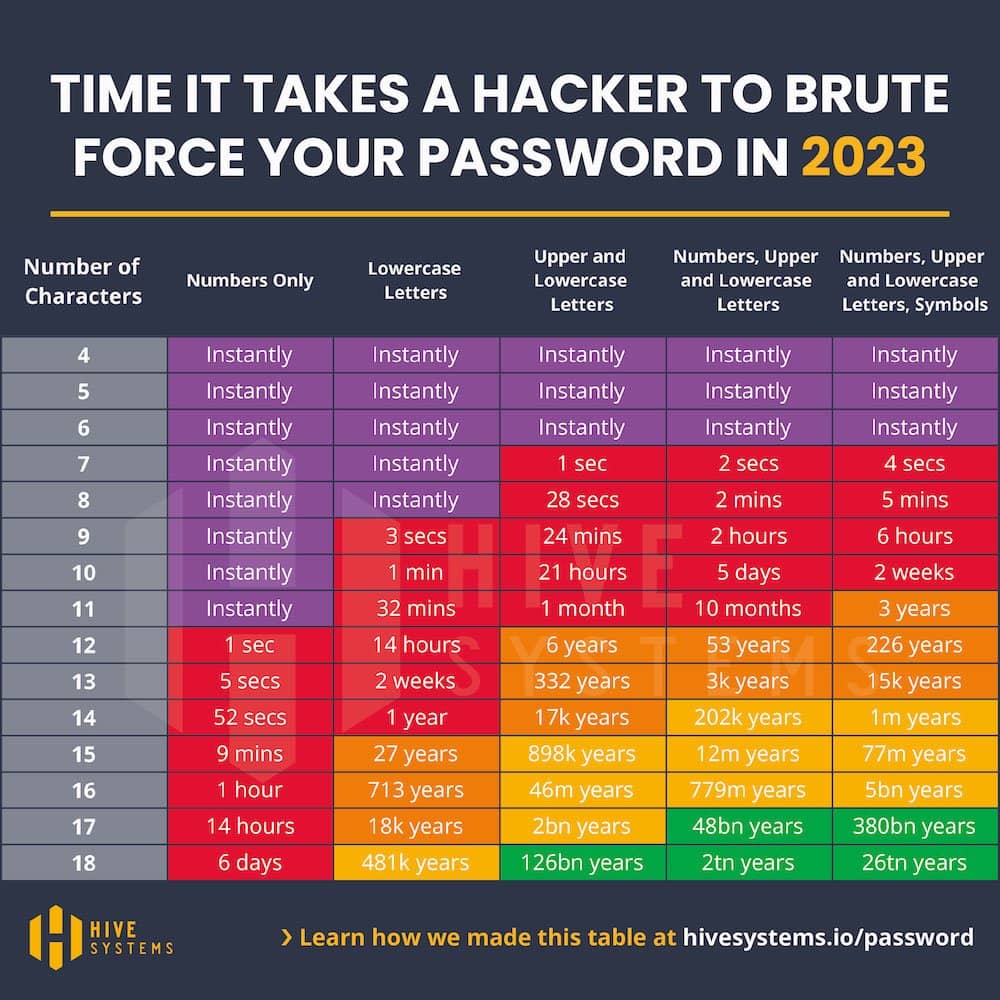
To give you a general idea of password strength, Hive Systems created a table (and regularly updates it) showing how long it will take to crack passwords based on their length and composition. For more details, read their blog post. Below is the 2023 table, which assumes use of the MD5 hash function and a computer built with 12 RTX 4090 GPU chips. As you can see, a hacker can crack even a random password of eight characters in under five minutes. Increase that to ten characters and the time goes to two weeks. Each additional character adds substantially to the time required. That’s why I recommend a minimum of 12 characters, but preferably more.
Unique Passwords
You now understand what makes passwords strong and why they are a key to password security. But what happens if a hacker gets one of your passwords? If you only used that password for one account, your exposure is limited, but if you used it across multiple accounts, you have put all of those accounts at risk as well. That’s why all security experts say that having unique passwords is a second key to password security.
From now on, make a habit of always creating unique passwords. But what if you already reuse passwords? Ideally, you should change them, but that may not be convenient or always necessary, especially for sites that don’t store any sensitive information. At a minimum, however, ensure you change any reused passwords for accounts that save sensitive information, especially for banking, email, and social media. And, of course, make sure any new or changed passwords are strong.
Creating, Saving, and Using Passwords
Ideally, all your passwords should be NICE:
- New (not reused between sites),
- Impersonal (don’t include common words or numbers),
- Complex (mixed-case letters, numbers, and special characters), and
- Extensive (at least 12 characters).
Unfortunately, the human mind isn’t great at creating and managing NICE passwords. Fortunately, there are some tools and techniques that can help.
Online Password Generators
Various online and offline tools can generate NICE passwords for you. One good option is the Security.org Random Password Generator.
Password Managers

A more convenient way to create NICE passwords is to use a password manager, AKA a password vault. These make organizing, storing, and accessing all your account details convenient. They also have a password creation tool that lets you specify the number and type of characters to use. Using lowercase and uppercase letters, numbers, and special characters will suffice for most accounts. Since you are using the password manager to remember and easily access these passwords, there’s no reason not to make them fairly long, say 20 characters (unless a site requires fewer).
Password managers have other useful features as well. They can usually check the strength of your existing passwords, work across devices, integrate with your browser or mobile apps, set inactivity timeouts, save usage history, scan for compromised accounts, and import accounts from another manager. Some also support multi-factor authorization, let you require the master password when accessing sensitive accounts, offer a family plan, can revoke device access from anywhere, can handle multi-page logins, and support passkeys.
Password managers protect your data with a master password, so you’ll want that to not only be NICE, but also memorable. One good option is a passphrase, which is a random string of words. Whatever master password you choose, consider what you will do if you forget it, since it holds the key to all your other accounts. It may be worth storing securely in plain text. That could be on paper, locked away somewhere safe or in an encrypted file.
Most password managers are paid or freemium products but a few good ones are free. The best free programs are KeePass (MacPass or OneKeePass for Macs), Bitwarden, and Password Safe.
Google Account Password Manager is another free option, but it is only useful if you use the Chrome browser and have an Android phone. Even then, it’s not a full-featured password manager, so you are probably better off with another option.
Apple Keychain is a free option that works on Macs, but it only supports Safari and Chrome running macOS Sonoma or later. It also works on Windows via a dedicated iCloud app and browser extensions for Chrome and Edge, but it doesn’t work with Firefox.
The major browsers (Chrome, Edge, Firefox) also include free password managers. Is using one a good option? In the past, I would have said no because they were weak about security and lacked important features (e.g., working with mobile apps, not just the browser). That’s not the case these days, though there are a few things that make me still prefer and recommend third-party managers. My biggest concern is that browser password managers rely on your syncing account rather than a master password. If that is compromised, so are all your passwords. You can set a separate master passphrase, but that’s not the default when getting started and figuring out how to do so isn’t obvious. Another concern is that it will lock you into using one browser. You can import passwords from one to another, but if you use more than one regularly, there is no way to sync changes between them. Finally, third-party password managers offer a lot more features. Still, if you’re not willing to put in the effort needed to choose and use a third-party tool, using your preferred browser’s password manager is certainly better than not using any manager tool at all.
| Browser Tip: If you choose to use a third-party password manager, disable the “remember password” feature in all your browsers. |
If you don’t like the idea of using your browser and none of the free tools appeals to you, you can check out a freemium option. From what I have read, Zoho Vault is the only freemium product that has a useful free version (most others limit the number of devices, integrations, or features).
Of course, a paid product may have features or usability you prefer. The most popular of these are 1Password, Dashlane, Keeper, LastPass, Keeper Password Manager & Digital Vault, NordPass, Norton Password Manager, Password Boss, RoboForm, and SplashID.
If you are curious, I am a long-time user of KeePass. It’s not the prettiest option but I like that it is open source and portable, it supports plugins, it can work with my browser (using KeeFox for Firefox, ChromeIPass for Chrome and KeeForm for Microsoft Edge), and it has mobile versions (KeePassDroid for Android and several for iOS, though I use MiniKeePass). I also like that it stores data locally rather than on a private company’s server. In addition, KeePass prevents dictionary attacks against your master password, keeps your passwords encrypted while the program is running, and has security-enhanced password edit controls. You can use a key file instead of a master password for increased security or combine the key file and password methods to further secure your data.
| Tip: A password manager is not just useful for storing passwords. It is also very handy for storing notes you want to keep secure. For example, I keep my credit cards, passport, driver’s license, Wi-Fi passwords, and other useful, but sensitive information. |
Whichever password manager you choose, take some time to explore all its options. I also recommend you regularly back up the contents of your password manager. Some have an option to do this regularly (e.g., each time the contents change) and most can export in some other format that you can store securely elsewhere. This is also a good reason to make an entry for your master password in the manager tool itself. If you somehow forget it, you can open a backup to find it.
Passphrases and Algorithms
Do you prefer to trade some security for convenience by using memorable passwords on some of your accounts? If so, two useful methods that can create NICE passwords are passphrases and algorithms.
A passphrase is a collection of random words, preferably ones that aren’t in a dictionary of common words, names, places, song lyrics, or literature. The major benefit of passphrases is that they are easier to remember than a collection of random characters. It’s also easy to make them quite long while still being memorable. That length by itself should make it strong, but obfuscate the words for added strength if so desired. If you are interested in understanding how passphrases compare to shorter, random character passwords, the Ask Leo article, “How Can Four Random Words Possibly Be More Secure Than 16 Random Characters?” does a good job explaining things.
One useful way to make your passphrase random is to use the Person-Action-Place method. Select a person who has some meaning to you, imagine that person doing something active, and consider an interesting place where the action takes place. This method is useful because our brains remember better with visual cues and with outlandish scenarios. Of course, you can also use technology to generate a passphrase for you. Two good online tools are Diceware and xkcd Password Generator.
Though remembering one or two passphrases is pretty easy, remembering many is not. Thus, an alternative strategy is to create passwords using an account-specific algorithm. By doing so, you create unique passwords and simply need to remember the algorithm to recreate them as needed.
The downside of using an algorithm is that it may be easy for someone to reverse engineer your algorithm. This could obviously be a problem, but if you choose a clever algorithm, it is not a likely scenario, especially if only one password is compromised. Also, remember that most hackers are not targeting you personally, so your password will mostly likely be compromised in a large-scale attack and sold as part of a large bundle of passwords. It’s unlikely that any person buying this data would take the time to isolate your account, recognize the password was likely created with an algorithm, and reverse engineer it.
Naturally, it’s hard to say how unlikely it is that a bad actor will reverse engineer your password algorithm. Use your best judgment and decide whether and where to use an algorithm based on your personal risk profile. I recommend you create truly unique and strong passwords (perhaps passphrases) for sensitive accounts and use an algorithm for not-so-sensitive accounts.
If you are curious about what an algorithm looks like, here’s an example.
Start by taking the last few characters of a site, app or account name in reverse order and capitalize the letters. For example, gmail.com would be LIA. Next, add to that a constant number (e.g., 5) and the number of characters in the URL (gmail.com is nine characters), resulting in LIA59. Next, add one or more special characters (e.g., #$). For example, LIA59#$. Next, take the first few characters of the site name, in lower case and enclose them in brackets. Again, for Gmail.com it would be {gma}. Add that to the previous string, yielding LIA59#${gma}. Now you have a 12-character password comprising mixed-case letters, at least one number, and multiple special characters.
Keep in mind that you may need to change your algorithm to accommodate password requirements or restrictions on certain accounts. You may also want to have different algorithms for different types of accounts and consider how you will handle accounts that require you to change the password regularly.
Saving Passwords
As your collection of accounts grows, consider how to manage them all. Obviously, a password manager is perfect for this purpose. Still, you may prefer to mostly rely on your memory if you use algorithms to create your passwords or you may prefer to write them all down, either by hand or electronically. Both methods leave you vulnerable to theft, though that risk can be significantly reduced if you store the paper list in a location protected by a lock or if you use a password to protect the spreadsheet or electronic file you use.
A practical downside of both written and electronic lists is that you may not have easy access to them when you are using mobile devices. And if you do, they are much more susceptible to theft. A paper list has yet another downside: the difficulty of looking at, and then entering, random strings of text. This difficulty may even lead you to avoid using strong passwords.
If you wish to keep a paper copy of your passwords, one useful tip is to write hints that will help you remember the password, rather than the password itself. This is easier to do if you used passphrases or an algorithm to create your passwords.
Password Limitations
One problem with any password creation strategy you may choose is that different websites impose different rules. Usually, these rules focus on the number and types of characters you can use. You can imagine the problems this may cause. For example, if your preferred strategy is to use a string of words to create a new password, it may be too long. Or if you prefer to separate those words with spaces, those spaces may not be allowed on some websites. Alternatively, if you use an algorithm that includes certain special characters, one or more of them may be prohibited. Whatever primary strategy you use to create new passwords, be prepared to have backup strategies if a website’s password restrictions make it necessary.
Changing Passwords
Another password restriction some accounts impose is requiring you to change your password regularly. I don’t see how this is helpful, as nothing about the age of a password makes it less secure over time, but it happens. If you use a password manager or a passphrase approach to create passwords, this requirement won’t likely be a problem, but if you use an algorithm, it will probably not work when you need to change your password.
Aside from being forced to change your password, there are situations where you might want to. Specifically, audit your current passwords and change any that are weak or reused. Also, change if you notice strange activity with an account. If you break up with someone you’ve shared accounts with, change those passwords; if you shared a computer, change all of your passwords.
Obviously, you’ll want to change any password associated with a hacked or otherwise compromised account, but how can you know if an account has been compromised? Popular services usually have public announcements when their servers are breached, but it is possible that you miss this announcement or no announcement is made and thus one of your accounts has been compromised without your knowledge. Fortunately, there are a few ways to check and monitor account hacks.
The website Have I Been Pwned? lets you check if a breach has exposed your email address (pwn is a slang term derived from the verb own, meaning to appropriate or to conquer to gain ownership). It offers an added service where you can sign up to be notified when future breaches occur. You can also check your passwords to see if they have been compromised in a past data breach. If you use my preferred password manager, KeePass, it offers multiple breach plugins that integrate with Have I Been Pwned? so you can easily look for breaches based on site/service, username, or password.
If you primarily use Google’s Chrome browser, it has a built-in feature that will notify you when you try to login to a site with a compromised password. It also works with the Google Account Password Manager to let you check any saved passwords.
Firefox has a similar service called Monitor that works with the Have I Been Pwned? database. You can use it to check any email address or you can sign in with a Firefox account and sign up for active monitoring of up to five email addresses.
If you learn of a breach that affects an account linked to other accounts (e.g., your email account) then consider changing the linked account passwords as well.
Password-Related Issues
Password advice deserves all the attention it gets, but securing your accounts also requires paying attention to usernames, email addresses, and extra authentication methods.
Usernames
Most advice about passwords ignores usernames but most people use the same username across sites when possible. Having unique usernames isn’t critical if you already use unique passwords, but it might help even if you do and definitely will help if you don’t.
You can use your password manager to create random, unique usernames, but you may prefer a way to remember them easily. If so, using an algorithm is probably a good idea. And it can be pretty simple. For example, your preferred username + the last few letters of the site/service. By tying the algorithm to the site, you can re-create your username easily without having to rely on memory or your password manager.
Email Addresses
Email addresses go hand in hand with usernames and many times accounts require your username to be an email address. Whether that’s the case or not, the ideal situation is to use a unique email address for each account, or at least for each sensitive account. That may seem impractical, but actually it’s not.
The simplest, though not the most secure, solution is to use a Gmail account. If your primary account isn’t Gmail and you prefer not to switch, you can create a Gmail account just for new account registrations and easily forward it to your primary email address. Using Gmail, you can easily create aliases by appending characters with a decimal (.) or a plus (+) sign. Google ignores everything after the plus or period and treats it like your regular address, but most sites will see them as distinct addresses. Of course, a malicious site or service will probably know this, but it is more a tactic for privacy than security. For example, if your Gmail address is [email protected] and you wanted to create a unique email address for each site based on the simple algorithm I just mentioned (appending the last three letters of the URL), your username for lifehacker.com would be [email protected]. The address [email protected] is functionally equivalent.
A second option is to use “throwaway” or “mask” e-mail addresses. Multiple providers offer these, but probably the best option is DuckDuckGo. It offers you two types of email addresses. The first is a personal address. You pick the name, and it never changes (for example, [email protected]). The second is a private, uniquely generated address. Both forward their emails to a primary address you specify and offer additional security features, like scrubbing emails of any trackers and preventing link tracking. This service integrates into your computer browser via an addon or extension (Chrome, Firefox, Edge) so whenever you register on a site that requires an email address, you can quickly choose a new one from the email field (or create one from the extension). To use on your mobile device, you will need to install the DuckDuckGo browser (Android, iOS).
Firefox Relay is a similar option if you use the Firefox browser (and it can mask phone numbers too). You can use it with other browsers as well, but you need to login in to your Relay dashboard, which is less convenient, and it only offers five free masks (paid plans can increase this amount).
If you have Apple products and use iCloud+ (any paid iCloud plan), you can use the Hide My Email feature. It will let you generate unique burner email addresses for free.
Yet another option is Burner Mail, which works with Firefox, Chrome, Android, and iOS.
Other, less convenient options exist as well, including 10 Minute Mail, Guerrilla Mail, and YOPmail. I say less convenient because they don’t integrate with your browser or have mobile apps. Typically, you visit their site to see a temporary email you can use. You stay on that page and it will automatically show you when an email is received for that temporary address. Use the confirmation details, delete the email, close the page and you are done. Most of the addresses provided are only valid for a limited time so they aren’t ideal for important accounts that may need to periodically send you emails (or for which you may want to reset your password someday). Some services, however, allow you to extend the life of the address.
Security Questions and Answers
When you create a new account or update an existing one, carefully consider any security question offered or required. Typically, a service will ask a security question like, “What is your mother’s maiden name?” The problem is that this information is easily found online or via social engineering. One solution is to use a security question that has an uncommon answer. However, many services provide only a limited choice of questions. In that case, consider using blogger Danah Boyd’s security question algorithm or use a false answer to a common question. You can also use your password manager to create a password and use that as the answer. Whatever security questions you choose, make the answers hard to guess but easy to remember and/or make a note of the answers in your password manager entry for that account.
Enable Two-Factor Authentication (2FA)
Multi-factor authentication (MFA), often called two-factor authentication (2FA), refers to requiring two or more pieces of evidence (or factors) before allowing someone to access a website or application. It’s based on the premise that an unauthorized person cannot supply both factors required for access. Typically, the first factor is something you know, i.e., your password, and the second factor is:
- Something you have: any physical object in your possession, such as an authenticator (e.g., mobile device), security token (e.g., YubiKey), a bank card, a key, etc.
- Something you are: some physical characteristic (biometrics), such as a fingerprint, eye iris, voice, typing speed, pattern in key press intervals, etc.
The most common second factor for online accounts is a one-time password (OTP) or verification code. This is typically sent to your phone or email or generated via an authenticator app like Authy or Google Authenticator.
2FA is not without downsides. Besides the general inconvenience of setup and use, OTPs can be intercepted or rerouted, and your mobile device can get lost, damaged, or stolen (or be without service). Plus, many systems that use OTPs do not securely implement them, and attackers may still learn the code through phishing attacks. Having said that, some services have taken steps to alleviate these concerns.
For example, Google can remember your computer so that you will only have to enter a verification code every 30 days. You can also specify a backup phone number (friend, family member) to use in the case your phone is unavailable for whatever reason. If all else fails, you can print out 10 one-time rescue codes, each of which you can use if you cannot receive or generate an OTP.
Thus, despite the potential downsides of two-factor authentication, it’s more secure than just using a password, so you should use it when possible. Although not every online service offers 2FA, an increasing number do, including most sensitive services you are likely using. As for which 2FA method you should choose, always use an authenticator app if available. These apps generate the verification code so they work offline and are more secure. Authy, in particular, can work on multiple devices, so if you lost one device you can use another as the backup. It’s also easy to move Authy to a new phone.
Social Login (OAuth and OpenID)

You have most likely noticed the option of registering with sites using your Apple, Google, or Facebook account rather than creating a new registration. This social login (aka single sign on) service is made possible by either OpenID or OAuth software standards. Comparing the two, OpenID uses a single set of user credentials to access multiple sites, while OAuth facilitates the authorization of one site to access and use information related to your account on another site.
The key question about social login is, should you use it? The answer, as with so many things, depends. On one hand, using social login is more secure than creating a new account because the website you are using will never see or store your password. By using social login, you only have to rely on a service you already trust (e.g., Apple, Google, Microsoft, X, Facebook) to protect your login credentials, and that service is likely in a better position to do so than whatever site you are accessing.
So, from a security point of view, it makes sense. On the other hand, you usually have to grant certain permissions to any site you access via your social account. These permissions (e.g., the ability to post, access your contacts, control your camera, etc.) may be more than you are comfortable giving. You also forego any anonymity when commenting or adding any content. The good news, however, is that each social service lets you easily sever the connection or change permissions to any site or app you have already authorized. In fact, if you regularly use social login, it’s a good idea to occasionally revisit your authorizations and revoke those that you no longer wish to use.
A compromise to get the extra security that social login represents but without the privacy concerns, is to create a dummy account with Google, Facebook or X and use it for authorizing sites. The downside to this is that you may have to logout of your legitimate account and into your dummy account to authorize a site, which can be a hassle (though Google now lets you switch between accounts easily).
Passkeys
Passkeys are relatively new as of this writing, so you may not have heard of them. One goal of passkeys is to get rid of the need for passwords entirely. That sounds pretty audacious, right? Let’s take a deeper look at this new security development.
Passkeys are designed to be more convenient and phishing-resistant than password authentication by using possession of a device or security key. The built-in authentication method for this device or key proves your identity. There’s nothing for you to remember (the device remembers the private key) and even if a hacker gets your public key in a data breach, it’s useless without also having the private key from your device. Of course, you need to keep your devices secure, but even if a hacker gets your device, the private keys might still be safe because they are stored securely and typically locked by default.
When you need to use a passkey, you first authenticate yourself with your device. If the hacker has your device but not its authentication method (password or biometrics) your accounts are still safe.
Without getting too technical, here’s how passkeys work. When you create a passkey, two cryptographic keys are created, a private key that lives on your device and a public key that lives with the service provider (e.g., Google, Microsoft). When you log into that service (or one that uses it as a social login), the server will query your device to make sure the keys actually match up, via the authentication method used to unlock the device itself. If the keys match, you gain access to the account or service.
| Want to know more? If you want more technical details, geared toward the layperson, Ask Leo has a good article, “What Is a Passkey?” |
Passkeys are becoming increasingly popular with the tech giants, so you’re likely to hear more and more about them. The latest versions of Android, iOS, macOS, and Windows already support them. Apple’s implementation uses Keychain if you use Safari or Chrome so you can then use the same passkey on all your Apple devices as long as you’re logged in to the same iCloud account. For Android or Windows, you’ll either need to create a passkey separately for each device or use a password manager that supports passkeys.
While the goal of passkeys is to replace password-based authentication, you can use them with new or existing accounts. In theory, new accounts won’t require a password at all, though I don’t know of any services that offer that yet. In the future, service providers may force you to abandon your password on an existing account (or use it only for account recovery), but for now, passkeys are mostly being used to make the authentication process more convenient and more secure.
For example, if you create a passkey for an existing password-based account and then want to log in into that account for the first time on a different device, you potentially have three options. First, you can log in as usual with your password. Second, you can confirm your login by acknowledging a prompt on a device where you’re already logged in. Third, you can confirm your login by clicking on a link or entering a code sent to the email address or phone of record for that account. Once you use one of these methods, a passkey for the new device will be created. That last option might sound familiar, especially if you use Google, which in October 2023 announced it will make passkeys the default log-in option for personal accounts (you can see your Google passkeys on the passkeys settings page). If you aren’t a Google user but another service has ever asked you to confirm a login on one device with another, that’s a passkey at work.
Computer Passwords

Most of the previous discussion focused on online accounts and services, but don’t neglect to add a password to your computer. To do so with Microsoft Windows, launch the Control Panel and select the User Accounts link. From there you can add or remove user accounts, change your account picture, or change your Windows password. It may also be a good idea to create a guest account if you plan to share your computer with others. For Mac OS, choose Apple menu > System Settings, then click Users & Groups in the sidebar (you may need to scroll down.)
A less commonly used security feature is a BIOS password. This will make circumventing a Windows password more difficult by requiring you to enter your BIOS password before Windows can even load. The exact method for doing this will vary by computer, so do a search online for your model.
| Note: If you install computer tracking and recovery software like Prey, you may actually prefer to allow a thief to access your computer. In such a case, the best option is to create an unprotected guest account. |
Click to Add the First »
